31 | Add to Reading ListSource URL: www.korugan.comLanguage: English - Date: 2014-12-23 13:10:14
|
|---|
32![Advanced Linux Firewalls Michael Rash Security Architect Enterasys Networks, Inc. http://www.cipherdyne.org[removed] Advanced Linux Firewalls Michael Rash Security Architect Enterasys Networks, Inc. http://www.cipherdyne.org[removed]](https://www.pdfsearch.io/img/f3675a9ea7181cc1daede8a2fae288dc.jpg) | Add to Reading ListSource URL: www.cipherdyne.orgLanguage: English - Date: 2013-11-03 15:37:36
|
|---|
33 | Add to Reading ListSource URL: www.korugan.comLanguage: English - Date: 2014-12-23 13:10:14
|
|---|
34 | Add to Reading ListSource URL: residential.iphantom.comLanguage: English - Date: 2014-08-08 22:42:29
|
|---|
35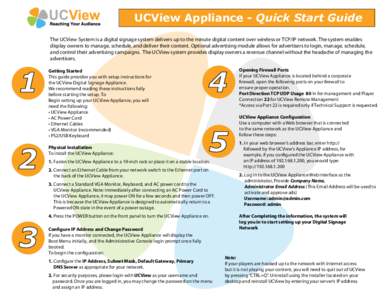 | Add to Reading ListSource URL: beta.ucview.comLanguage: English - Date: 2014-08-06 17:30:00
|
|---|
36 | Add to Reading ListSource URL: download.microsoft.comLanguage: English - Date: 2015-02-13 19:52:47
|
|---|
37 | Add to Reading ListSource URL: www.ciaops.comLanguage: English - Date: 2012-09-25 20:38:23
|
|---|
38 | Add to Reading ListSource URL: www.i7technologies.co.ukLanguage: English - Date: 2012-11-14 09:22:39
|
|---|
39![InJoy Firewall Firewall Security Guide 4.2 �Copyright © [removed], bww bitwise works GmbH.. All Rights Reserved. The use and copying of this product is InJoy Firewall Firewall Security Guide 4.2 �Copyright © [removed], bww bitwise works GmbH.. All Rights Reserved. The use and copying of this product is](https://www.pdfsearch.io/img/089b51252d73425318220d1bdb91038e.jpg) | Add to Reading ListSource URL: www.bitwiseworks.comLanguage: English - Date: 2014-02-25 08:50:45
|
|---|
40 | Add to Reading ListSource URL: www.edvancesecurity.comLanguage: English - Date: 2012-07-10 03:56:57
|
|---|